Endpoint Malware Protection
Introduction
This procedure guide is deprecated. It was written for the 3.7 version of VT’s Minimum Security Standard.
Using strong malware protection is important in keeping your device secure from vulnerabilities and attacks. This document will outline ways to ensure your device has malware protection.
Windows
Information on how to update your Windows system can be found in the knowledge base (KB) article on Endpoint Patching.
macOS
Information on how to update your macOS device can be found in the KB article on Endpoint Patching.
Notarization
According to Apple’s support website, notarization is defined as the following.
“Notarization is a malware scanning service provided by Apple. Developers who want to distribute apps for MacOS outside the App Store submit their apps for scanning as part of the distribution process. Apple scans this software for known malware and, if none is found, issues a Notarization ticket. Typically, developers staple this ticket to their app so Gatekeeper can verify and launch the app, even offline.”
This process ensures software that is on the Apple App store is safe to use on Apple computers and systems. Notarization runs automatically on your Apple system, so configuration is generally not required.
XProtect
XProtect is a built in antivirus software designed to make sure software that may contain malware is not executed on an Apple system. XProtect scans software every time that software is launched, changed, or the XProtect systems signatures are updated.
Linux
One of the easiest ways to prevent malware from infecting your Linux system is to make sure the system is up to date. Information on how to update your various Linux systems can be found in the KB article on Endpoint Patching.
Additionally, it can be beneficial to enable automatic security updates to avoid having to remember to update frequently. Review the following documentation on automatic security updates for your Linux distribution.
- Ubuntu Automatic Security Updates
- Debian Automatic Security Updates
- Fedora Automatic Security Updates
Install Programs from Official Channels
A common vector for malware on Linux systems is third-party program sources. Thus, it is important that software be installed from package repositories that come by default with Linux distributions. These include:
- Ubuntu: The official Ubuntu repositories
main,restricted,universe, andmultiverse. Software from the Ubuntu Software Center come from official repositories and are therefore also safe. - Debian: The official Debian repositories
stable,main,contrib, andnon-free. - Fedora: The official Fedora repositories
fedoraandupdates.
Packages in the default repositories of each distribution are curated, verified, and vetted by developers of their respective distributions. Packages from third parties should therefore be avoided whenever possible. For the systems listed above, these include:
- Ubuntu: Third-party repositories and Personal Package Archives (PPAs).
- Debian: Third-party repositories.
- Fedora: Third-party repositories.
These sources do not undergo the same process of validation as packages in official repositories. Installation is at the risk of the user. If a piece of software you wish to install cannot be found in the official repositories, some safer alternatives to third-party repositories include Flathub and Snapcraft.
These two sources provide applications in the form of Flatpaks and Snaps respectively, which are self-contained applications run in a sandbox. Thus, they have limited access to the host system, reducing the possibility of malware. Additionally, Snap and Snapcraft are developed by Canonical, the company behind Ubuntu.
Packages from Flathub and Snapcraft are not subject to the same scrutiny as packages from official Linux repositories. It is recommended to only install packages from publishers you trust.
Linux Antivirus Software
If you wish to use antivirus software to protect your Linux machine, there are a few recommended programs by distributions:
- Ubuntu Antivirus
- Open source: ClamAV Antivirus, ClamTK.
- Closed source: Avast Core Security, GRAVITYZONE ENTERPRISE SECURITY, ESET NOD32 Antivirus Business Edition for Linux Desktop, XFProt, Sophos Antivirus for Linux, Symantec Endpoint Protection.
- Securing Debian
- ClamAV Antivirus - anti-virus utility for Unix - command-line interface.
- ClamTK - A graphical user interface for ClamAV (depends on ClamAV).
- mailscanner - “an e-mail gateway virus scanner and spam detector.”
- amavis-ng - “a mail virus scanner which integrates with different MTA (Exim, Sendmail, Postfix, or Qmail) and supports over 15 virus scanning engines.”
- procmail - " a tool that uses the procmail package, which can scan email attachments for viruses, block attachments based on their filenames, and more."
- exiscan - “an e-mail virus scanner written in Perl that works with Exim.”
- blackhole-qmail - “a spam filter for Qmail with built-in support for Clamav.”
Fedora does not recommend any specific antivirus software, however the software listed above should work on Fedora systems too.
For a basic antivirus that is recommended and easy to use, ClamAV Antivirus works on most Linux distributions. See below for a guide on ClamTK, a GUI frontend to ClamAV Antivirus.
Instructions
Using Windows Defender Antivirus
- Search “Windows Security” in the Windows Search Bar.
- Click Virus & Threat Protection.
- Here you will see multiple options that will help protect your Windows System.
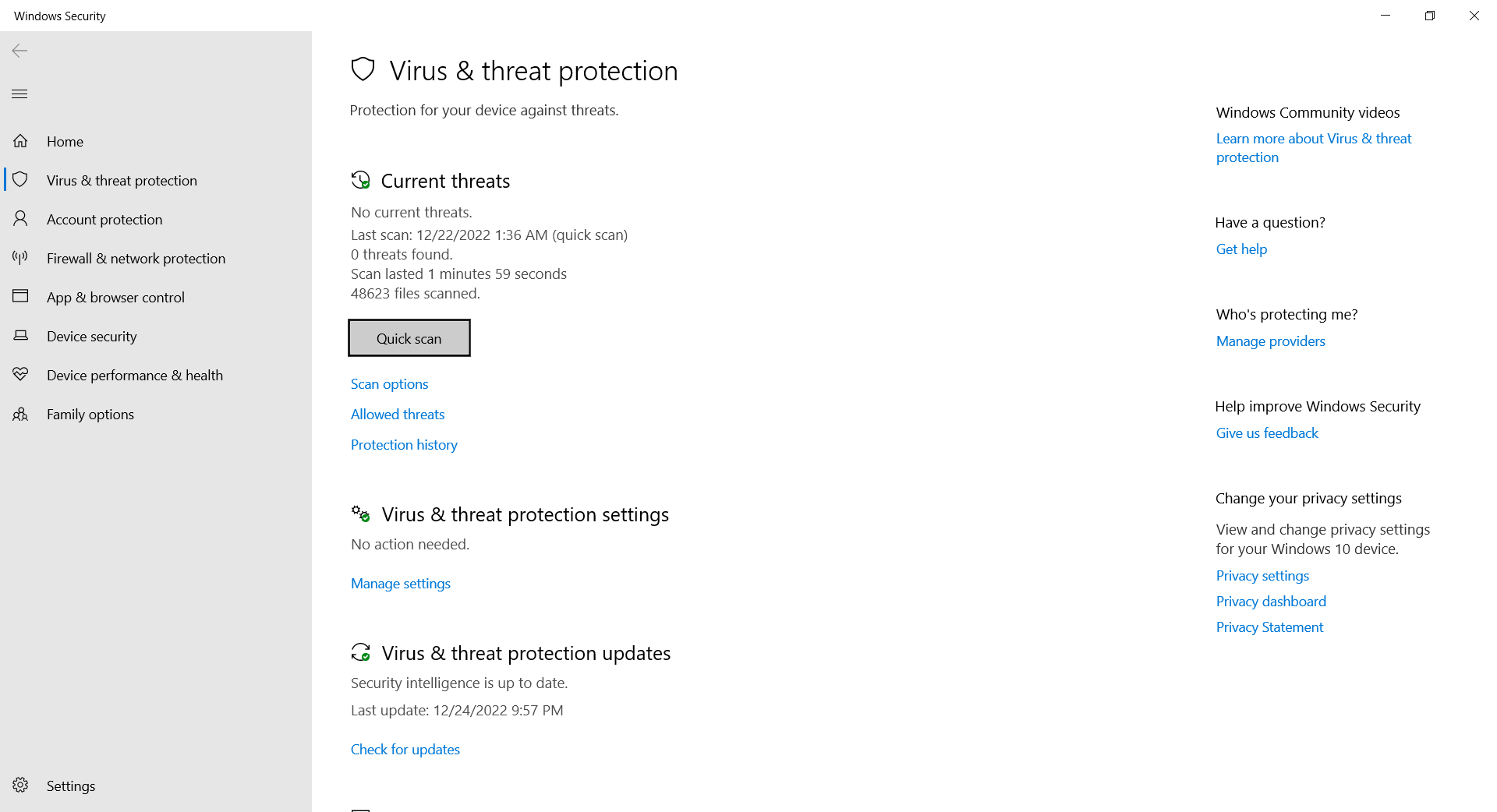
- Current Threats: This option will display any current threats to your system, and allow you to scan your system for more.
- Virus & threat protection settings: This option allows you to change various settings for the antivirus software. Changing these settings is generally not needed for day-to-day use.
- Ransomware Protection: See the guide below on how to use ransomware protection.
Using Ransomware Protection on Windows
Windows Ransomware Protection involves two main components: Controlled Folder Access and Ransomware Data Recovery. These components can be accessed by going to Windows Security > Virus & Threat Protection Settings, then clicking on Manage ransomware protection under the Ransomware Protection section.
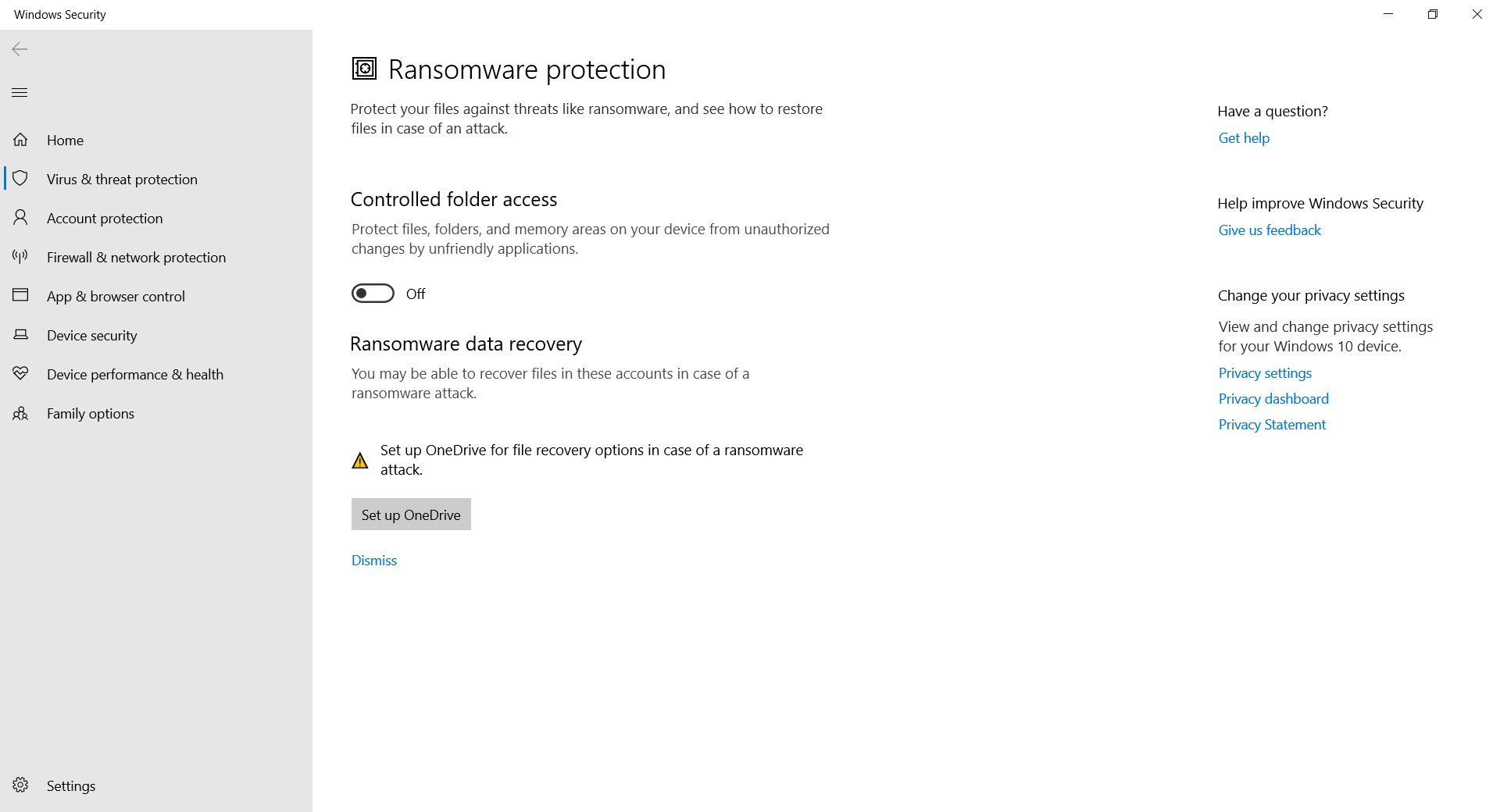
Controlled Folder Access
Controlled Folder Access lets you prevent unauthorized changes to certain files and folders from applications you do not allow.
- To enable, ensure the toggle for Controlled Folder Access is switched on.
- Once enabled, three links should appear below the toggle.
- Block history displays activity on the most recently blocked programs due to Controlled Folder Access.
- Protected folders allows you to add or remove files and folders protected by Controlled Folder Access. Windows system folders are protected by default.
- Allow an app through controlled folder access allows you to whitelist an application blocked by Windows.
Ransomware Data Recovery
Ransomware data recovery allows you to back up files onto Microsoft’s OneDrive in case your files become compromised. To utilize this service, click Set up OneDrive if you haven’t already, otherwise click View files to ensure files you want kept safe are present.
Ensure files backed up to OneDrive to meet the Security and Data Protection policies set by the Division of IT.
Preventing Malware
Windows
- Keep your system up to date.
- Use Windows’ built-in malware protection, Windows Defender Antivirus.
- (Recommended) Use separate anti-malware software in addition to the protections that come with Windows. Some of these can be found on the Windows App Store, but be sure to only install software that you trust.
macOS
- Keep your system updated.
- Apple describes a three-layer defense system on their support website. This defense system takes care of malware protection for you.
- Prevent launch or execution of malware.
- Block malware from running on the system.
- Remediate executed malware.
- Apple systems have three programs designed to carry out these steps.
Linux
Linux is generally less prone to malware for the following reasons:
- Software is usually ran as a normal user, which has limited capabilities if configured correctly.
- Most software ran on Linux systems are open source.
- Linux system configurations can be very diverse and different.
Despite this it is still a good idea to keep your Linux system safe through these practices:
- Ensure your system is kept up-to-date.
- Install programs from official channels wherever possible. Limit program installation from third-party repositories or untrusted channels.
- (Optional) Install antivirus software on your machine.
Installing ClamTK
ClamTK allows users to easily use ClamAV’s features in a graphical user interface. ClamAV has a variety of useful features to allow users to secure their Linux system.
Installation on Ubuntu (22.04LTS)
ClamTK can be installed via the command line using the apt-get command.
sudo apt-get install clamtk
Installation on Debian
ClamTK can be installed via the command line using the apt-get command.
sudo apt-get install clamtk
Installation on Fedora
ClamTK can be installed via the command line using either dnf or yum.
DNF
sudo dnf install clamtk
YUM
sudo yum install clamtk
Navigating ClamTK
- Settings: Generally the default settings will be sufficient for day-to-day use, however you can configure a few aspects of ClamAV such as when to update, and what files to scan.
- Whitelist: The whitelist allows you to prevent ClamAV from scanning them.
- Network: Network allows you to set up a proxy.
- Scheduler: Scheduler allows you to specify when ClamAV will complete its scan and when to update its signatures.
- History: History will give you a history of any files it may have found that contain some form of virus or malware.
- Quarantine: This allows you to quarantine any files that may be dangerous.
- Update: Allows you to update the antivirus.
- Update Assistant: Allows you to define how to update your antivirus signatures.
- Scan a file: Have ClamAV scan a file.
- Scan a directory: Have ClamAV scan a directory.
- Analysis: Complete further analysis of files or directories.


